Meltdown & Spectre: Analyzing Performance Impacts on Intel's NUC7i7BNH
by Ganesh T S on March 23, 2018 4:15 PM EST- Posted in
- Systems
- Spectre
- Benchmarks
- Meltdown

One of the consequences of the Meltdown and Spectre vulnerabilities, besides the immediate security concerns, is what it has meant for our ongoing testing and benchmarking operations. Along with accounting for the immediate performance changes from the required patches, we've also needed to look at how we present data and how we can (or can't) compare new patched systems to older unpatched systems. From an editorial perspective we need to ensure the continuity of our data as well as providing meaningful benchmark collections.
What we've found so far is that the impact of the Meltdown and Spectre patches varies with the workload and the type of test. Nate's GPU testing shrugs it off almost entirely, while Billy's SSD testing especially feels the pinch. In the middle of course are consumer system reviews, where workloads are more varied but also much more realistic and often more relevant as well. Of course, this is also the type hardware that we most often have to return when we're done, making it the most challenging to correct.
As everyone at AnandTech has been integrating the patches and updating their datasets in their own way, I wanted to offer some insight into what's going on for system testing. With several important systems set to launch in the first half of this year – particularly Intel's Hades Canyon – I've been going back and collecting updated results for use in those future reviews. In the process, I also wanted to document how performance has been impacted by these security patches and which benchmarks in particular have been affected.
Evaluation Setup
The Intel Kaby Lake NUC (NUC7i7BNH) was used for all the benchmarks presented in this article. It was chosen for two reasons. Being a relatively new system that consumers can still purchase in the market, evaluating it presents data of particular relevance to readers. Intel was prompt in providing BIOS updates to resolve the Meltdown and Spectre issues compared to other OEMs whose systems I had in hand for evaluation. The NUC was configured with the following specifications:
| Intel NUC7i7BNH (Unpatched) Specifications | |
| Processor | Intel Core i7-7567U Kaby Lake-U, 2C/4T, 3.5 - 4.0 GHz, 14nm+, 4 MB L2, 28W TDP |
| Memory | Crucial Ballistix Sport LT BLS16G4S240FSD.16FAD DDR4 15-15-15-35 @ 2133 MHz 2x16 GB |
| Graphics | Intel Iris Plus Graphics 650 |
| Disk Drive(s) | ADATA SX8000NP (128 GB; M.2 Type 2280 PCIe 3.0 x4 NVMe; Micron 32L 3D MLC) |
| Networking | Intel Dual Band Wireless-AC 8260 (2x2 802.11ac - 866 Mbps) 1x Intel 10/100/1000 RJ-45 GbE |
| Audio | 3.5mm Headphone Jack Capable of 5.1/7.1 digital output with HD audio bitstreaming (HDMI) |
| Miscellaneous I/O Ports | 4x USB 3.0 Type-A 1x Thunderbolt 3 USB-C 1x micro-SDXC |
| Operating System | Retail unit is barebones, but we installed Windows 10 Enterprise x64 |
| Pricing (Barebones) | USD 445 |
| Full Specifications | Intel NUC7i7BNH Specifications |
Three different patch configurations were benchmarked:
- Completely unpatched
- Only OS patches activated (Graph entry : Patch OS)
- Completely patched with updates to both the OS and the CPU microcode (Graph entry : Patch OS + uCode)
While it will (eventually) be an uncommon configuration, right now a lot of systems are still only running OS patches without their associated microcode updates, as the latter is still being distributed. At the same time, because the microcode patches are primarily for Spectre – Meltdown fixes are implemented at an OS level – this allows us to see just how much of an impact the Spectre fixes have on top of the existing Meltdown fixes.
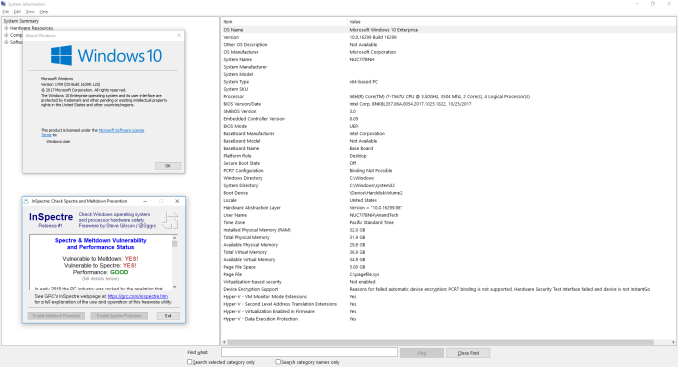
The completely unpatched system used Windows 10 version 16299.125 with BIOS v0054. As evident from the screenshot below, the system is susceptible to both Spectre and Meltdown.
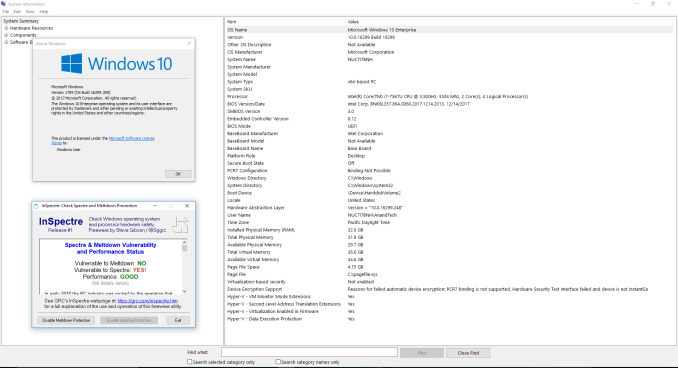
The second configuration was processed with Windows 10 version 16299.309 with BIOS v0060. The screenshot below shows that the system is protected against Meltdown, but, not Spectre.
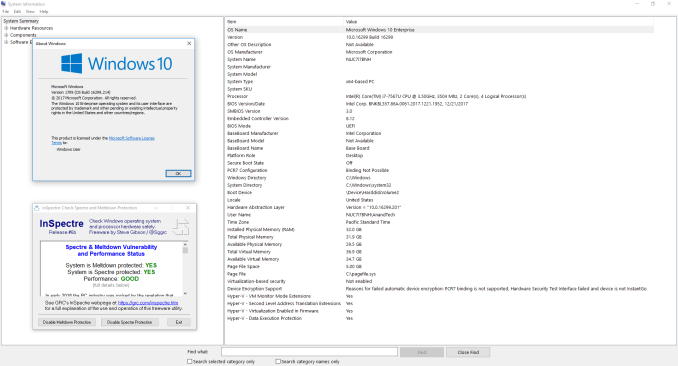
The final fully patched configuration was process with Windows 10 version 16299.214 and BIOS v0061. The current BIOS is v0062 (the one we used was available briefly before it was pulled to undergo additional QA for possible random restarts). This configuration shows full protection against both Meltdown and Spectre.
We used our standard test suite for low power desktops / industrial PCs in order to evaluate the impact of the patching on the performance of the system.










83 Comments
View All Comments
chuychopsuey - Friday, March 23, 2018 - link
Wow! That's pretty significant. Looks like it takes you a generation or two backwards.Samus - Saturday, March 24, 2018 - link
The real damage comes for people with NVMe SSD's or other CPU-centric PCIe hardware. 29% performance drop...wow.III-V - Saturday, March 24, 2018 - link
On a single benchmark.You might need to see an optometrist.
Samus - Sunday, March 25, 2018 - link
Optometrist, no. Optimist, yes.umano - Sunday, March 25, 2018 - link
I want to be optimist, this is not a very powerful cpu "This significant performance loss is partly due to the NVMe drive performance now being CPU bound" so maybe on more powerful cpu this % will be lower... I hope solinuxgeex - Monday, March 26, 2018 - link
yes but people with high-end CPUs will tend to have even faster drives, or RAID, or Optane as a disk cache, and I've seen benchmarks where Optane performance dropped >40% on i9. Desktop users won't feel this very much but others who have been paying 300% more for 25% more performance for scale-up business logic are crying.iter - Monday, March 26, 2018 - link
Ultra high performance is only required in workstations. Workstations are used for important work. It is best to keep such systems offline. No need for antivirus, firewall, updating, patching and all that stuff that impedes performance and introduces downtime.The maxima among professionals is "if it works don't touch it". We are well past the point where it is worth keeping everything up to date with the latest versions. It's been a while since version updates were about making things better for the user, they are mostly about making things better for the big software corporations.
Use a separate low end system for internet. With nothing important on it.
PeachNCream - Monday, March 26, 2018 - link
I can't think of any situations where I've seen professional workstations that are intentionally kept offline and deprived of software updates. Perhaps that's something that would happen in a small business or SOHO where the end user is also her own IT support and might make such an odd decision, but as a client to a company using that sort of policy, I'd be concerned they were making a larger error of judgement in adhering to automotive or mechanical engineering wisdom of the 20th Century.iter - Monday, March 26, 2018 - link
That same wisdom that has resulted in countless security breaches and the privacy of billions of people violated.Thanks but no thanks. The "standards" are too low.
The lack of internet connectivity doesn't in any way impede dedicated support personnel from supporting. Those people are supposed to know their biz, not google about it.
The only error in judgement you should be concerned at the time is your own. A system that is dedicated to doing work has no job being connected to the internet. There is absolutely no good reason to update it as long as it operates property. The update will add no value, will only introduce downtime, and is likely to break stuff up.
PeachNCream - Monday, March 26, 2018 - link
Despite those strongly expressed thoughts, there are very few workstations that are running as stand-alone systems that don't get vendor software updates.